Cybersecurity Incident Response Plan
Over the years, there has been a rapid increase in cyber-attack, now is the time for organizations should be abreast of the threats and come out with written documents or response plans to deal with cybercriminals.
This article will lay out the meaning of the incident response plan, the steps of incident response, and why an incident response plan is so important. If you want to learn, make sure read the post.
What is an incident response plan?
An incident response plan: is a set of written documents that instruct IT professionals, use to identify any security breach and recover from cybersecurity threats. Incident response plans ensure quick responses in the event of cybersecurity possible. These plans are necessary to mitigate damage caused by cybercriminals, including data loss, and network attacks.
Incident response strategy planning typically includes:
i. The organization’s incident response strategy and how it supports the mission statement
ii. Goal setting and responsibilities involved in incident response
iii. Strategy for each phase of the incident response plan
iv. Channel of Communication whom to report to both internal and external stakeholder’s example: senior management, IT departments, board of directors, and customers or staff
v. Evaluation of previous incidents to improve the security of the organization
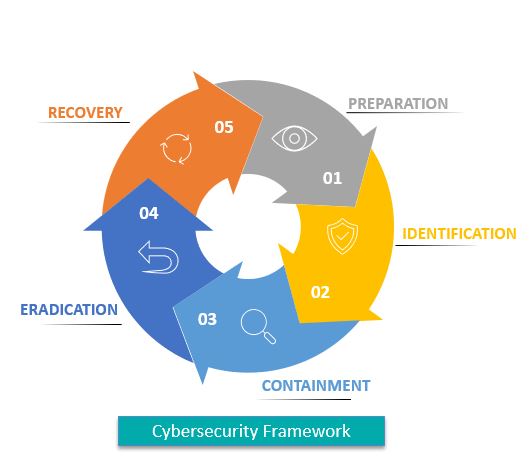
What are the five steps of an incident response plan?
The response plan should address and provide a structured process for these steps.
1. Preparation: Preparation Stage Firstly, you should outline and document the detailed security policy that informs your incident response plan. Identify and analyze security issues, in the event of a data breach develop a plan and prepare documentation that clearly and briefly states the roles, responsibilities, and processes to mitigate them.
2. Identification: The IT security team should be able to detect the breach and be able to respond and uses various threat intelligence streams, intrusion software system, and firewalls to mitigate the event of a cyberattack.
3. Containment:
Once the team discovered a security breach, the immediate goal is to contain the incident and prevent further damage from occurring. This involves:
i. Short-term containment — this can be as simple as disconnecting the affected network device that is under a cybersecurity attack.
ii. Long-term containment — applying a redundant system backup to help restore business operations sensitive data
4. Eradication: Cybersecurity personnel must identify the root cause of the incident, remove malware, and the systems patched are updated to prevent similar incident attacks in the future
5. Recovery: The IT team is to restore the affected systems and ensure another incident doesn’t take place.
Why is an incident response plan so important?
i. Data Protection is achieved by securing confidential data backups, and machine vulnerabilities are timely updated.
ii. The organization’s reputation is assured in teams of security and privacy
Again, You can read on Overview of Cybersecurity in Organization , Cybersecurity in Banking Fraud and Threat Intelligence in Cybersecurity
I will also recommend you read the post on How Does Cloud Computing Technology Work,Data protection in Cyber security, How Does Cloud Computing Technology Work, Turn ON or Off Two Factor(2F) Authentication for your Gmail using your Phone Number, Add alternative Email or Phone to Reset Account Password in the event of forgetting your Login credential , How to Use Google Translate and How to Login to Gmail Account, Sync Phone contact, Export Contacts from Gmail Account to Phone it could be of help.
Conclusion
Now, you must have an idea of Cybersecurity in Banking Fraud, Ask your questions in the comments below. Try to follow us on Facebook, Instagram , and Twitter. Also if the post has helped you Kindly subscribe to our YouTube channel to continue learning.

